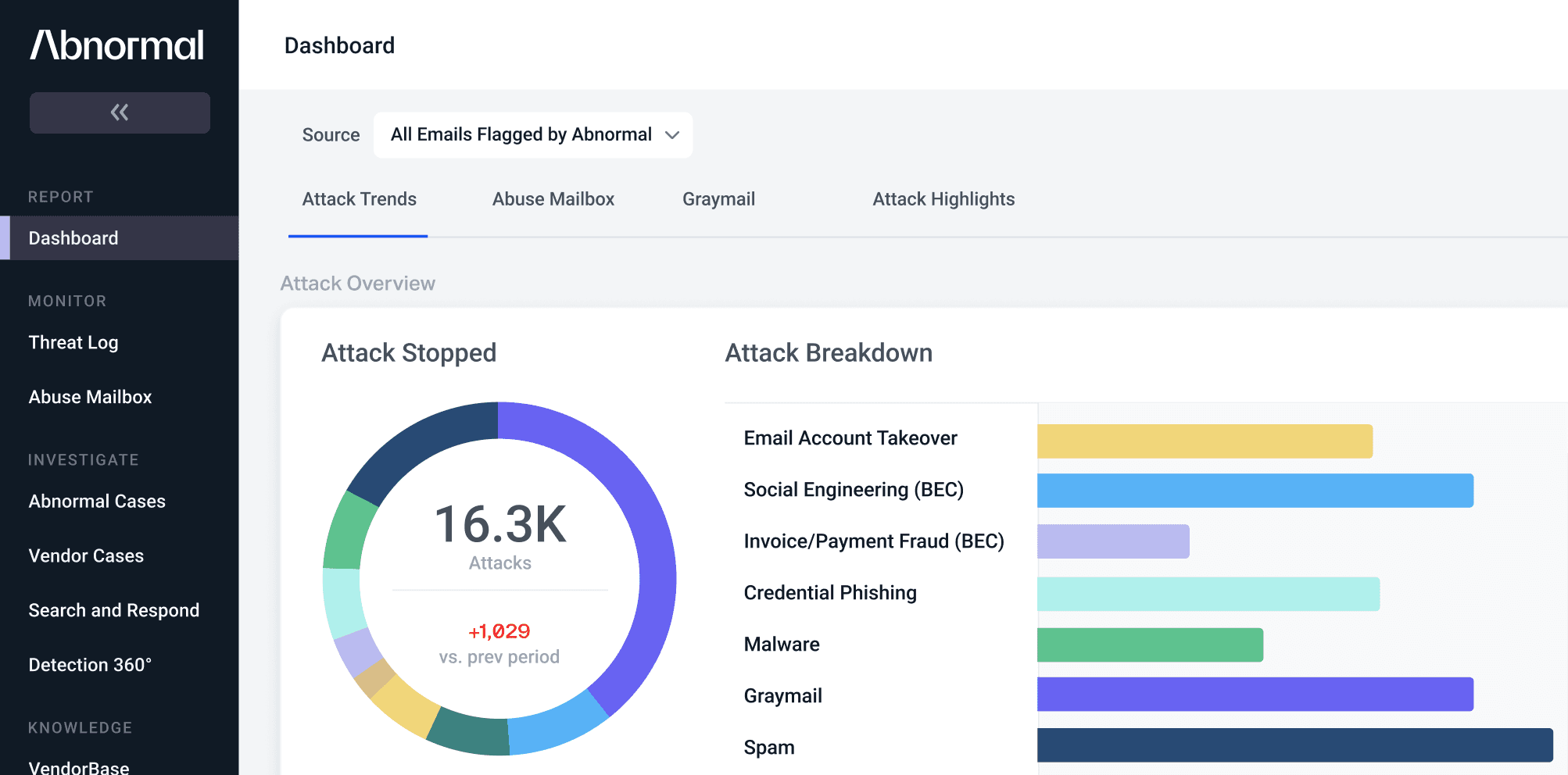
Adobe Acrobat Sign Impersonators Use Customized Phishing Pages in Email Attacks
Adobe has been a trusted name in business solutions for nearly four decades and is used by millions of professionals worldwide. The downside of this popularity is that it makes them an irresistible brand for cybercriminals to impersonate.
In a series of recent credential phishing attacks, threat actors convincingly impersonated Acrobat Sign, Adobe’s cloud-based e-signature service. Even more impressive is that the perpetrators built their own infrastructure to send the attacks, personalized each malicious message to the recipient, and created bespoke phishing pages that featured each targeted company’s own logo.
The threat actors targeted more than 250 organizations across multiple industries, including financial services, healthcare, retail, and more.
Breaking Down the Adobe Acrobat Sign Impersonation Attack
Designed to appear as a message sent via Adobe Acrobat Sign, the email claims that the employee's signature has been requested on a non-disclosure agreement (NDA) for their employer.
Malicious email imitating Adobe Acrobat Sign notification
The message includes a button labeled “Review and sign,” which, in an actual email sent using Adobe Acrobat Sign, redirects the user to a page to view the document. However, in this malicious message, the button is linked to a phishing site designed to look like a Microsoft 365 login page that is customized with the targeted company’s logo.
Phishing page engineered to resemble Microsoft 365 login portal with targeted company’s logo
Incorporating the organization’s logo into the fake Microsoft 365 sign-in screen supports the pretext that the initial email and all subsequent steps in the process were generated and are occurring within the targeted company’s own ecosystem.
Unfortunately, if the recipient believes the login prompt is real and enters their username and password, the threat actor will steal, save, and exploit their credentials—either to access other applications within the network or to launch additional attacks.
Why This Impersonation Attack Is Unique
Brand impersonation is a hallmark of credential phishing attacks. Threat actors pose as a myriad of different companies—from payment platforms and social media networks to shipping providers and even dating services. However, the level of sophistication—and, consequently, the degree of believability—in these attacks spans quite a broad spectrum.
What makes this series of attacks remarkable is that the fake version of the message is a striking replica of the actual Adobe emails. Cybercriminals will often sell customizable phishing email templates on darknet marketplaces to help other threat actors make their attacks more convincing. This likely seems to be the case here, as the branding and the formatting of the emails match the legitimate version especially well.
Example of non-malicious email sent via Adobe Acrobat Sign
Another noteworthy aspect of these attacks is that so many elements have been customized to the specific recipient. The subject line includes the names of the employee and their employer—as does the email body content. Even the phishing page is customized with the targeted company’s logo. This level of personalization was unheard of even five years ago, yet we’re beginning to see it increasing in frequency, such as in this Disney+ impersonation attack.
From a technical perspective, the threat actor built their own infrastructure and sent the attack using accounts that had been registered on lookalike domains—including acrobatsign[.]eu[.]com, acrobatsign[.]us[.]com, adobesign[.]de[.]com, adobesign[.]gr[.]com, and adobesl[.]com. This approach afforded them multiple benefits.
First, it enabled them to customize the sender display name and sending domain to include variations on the Adobe Acrobat Sign name, including “Acrobat Sign” and “Adobe Sign.” This allowed the attacker to enhance the appearance of authenticity, improving the probability of the recipients believing the notification was real. Additionally, because the domains were legitimate, the messages passed SPF, DKIM, and DMARC authentication, meaning they would be more likely to bypass traditional security solutions and land safely in inboxes.
What Makes This Attack Challenging to Detect
Older, legacy email security tools, such as secure email gateways (SEGs), struggle to accurately identify these emails as malicious for multiple reasons.
The first is due to the use of social engineering. Rather than focusing on technical vulnerabilities, socially engineered attacks rely on manipulation and deceit to exploit human psychology. Traditional security tools lack the functionality to understand the subtleties and nuance of language and human behavior, making it difficult to distinguish between genuine and malicious intent.
Additionally, the attackers leveraged newly registered domains that had never been used to send emails to the targets before. SEGs utilize historical data and reputation-based filters to detect malicious domains, but in this case, there was no negative history for a SEG to detect.
Further, while the emails did contain malicious links, they were obfuscated using an open redirect on two legitimate domains. Because traditional security solutions only analyze the top-level domain and not the entire URL, they wouldn’t detect the phishing links attached to the “safe” domains.
Blocking Impersonation Attacks with Behavioral AI
Unlike secure email gateways, an AI-native email security solution uses machine learning, behavioral AI, and content analysis to correctly identify these emails as malicious. It detects the impersonation of a brand, the use of social engineering, and the presence of malicious links as well as the fact that the emails were sent from an unknown sender.
With an anomaly detection engine that leverages identity and context, an AI-powered email security platform can stop this attack before it reaches end users.
To see how Abnormal AI provides comprehensive email protection against attacks that exploit human behavior, schedule your demo.
See the Abnormal Solution to the Email Security Problem
Protect your organization from the full spectrum of email attacks with Abnormal.